Explore the benefits and importance of functional testing in ensuring bug-free, user-friendly, and reliable software.
How does Functional Testing Improve Software Quality?


Explore the benefits and importance of functional testing in ensuring bug-free, user-friendly, and reliable software.

Dive deep into the world of software testing failures. Gain insights into the root causes behind common issues and learn how to overcome them for smoother development processes.

Learn how to avoid common software testing mistakes and enhance your testing process. Discover actionable tips to ensure smoother testing and deliver higher-quality software products.

Gain insight into the significance of functional testing in software development through this blog. Explore its crucial role in ensuring software quality and reliability, and learn best practices for implementation.
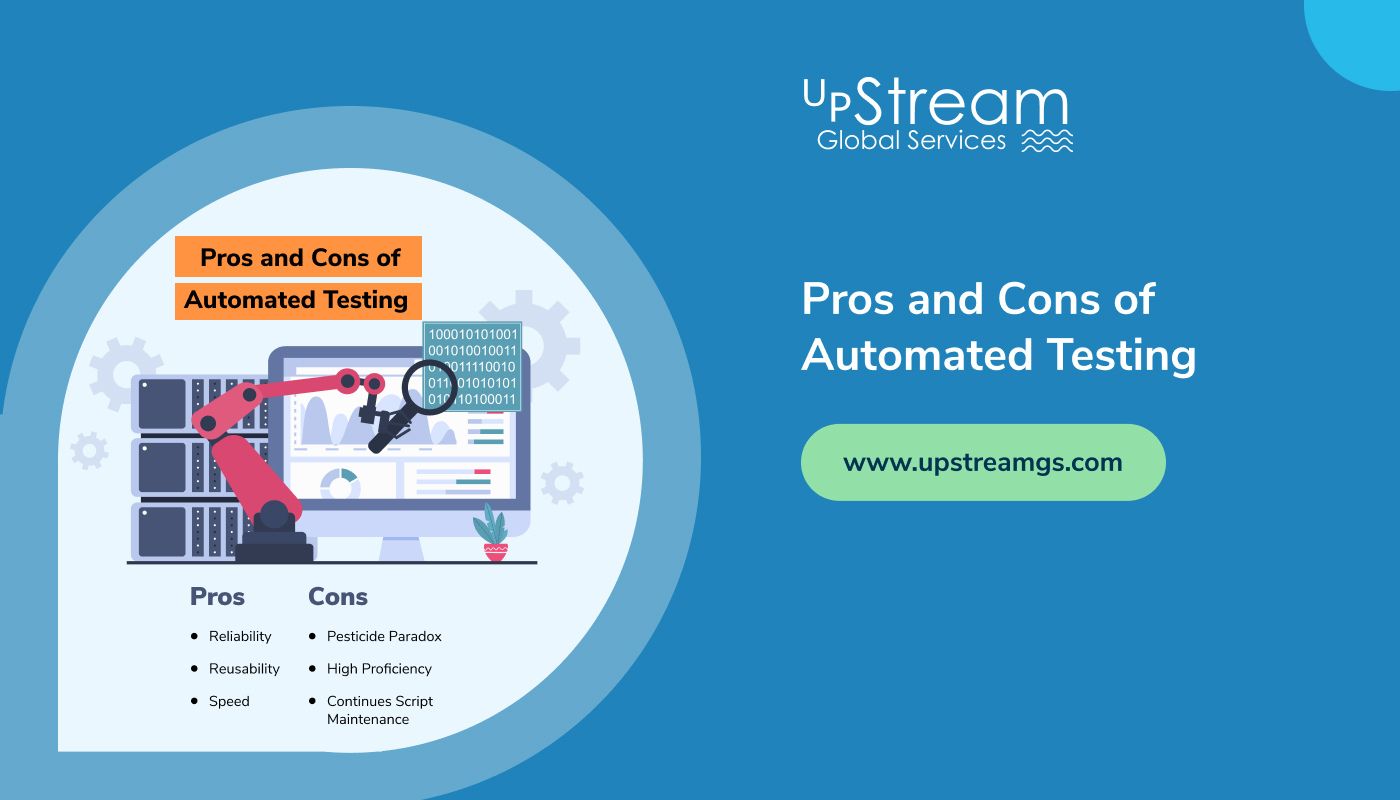
Discover the benefits and drawbacks of automated testing. Learn how it streamlines processes and enhances efficiency, while also exploring potential challenges and considerations for implementation.
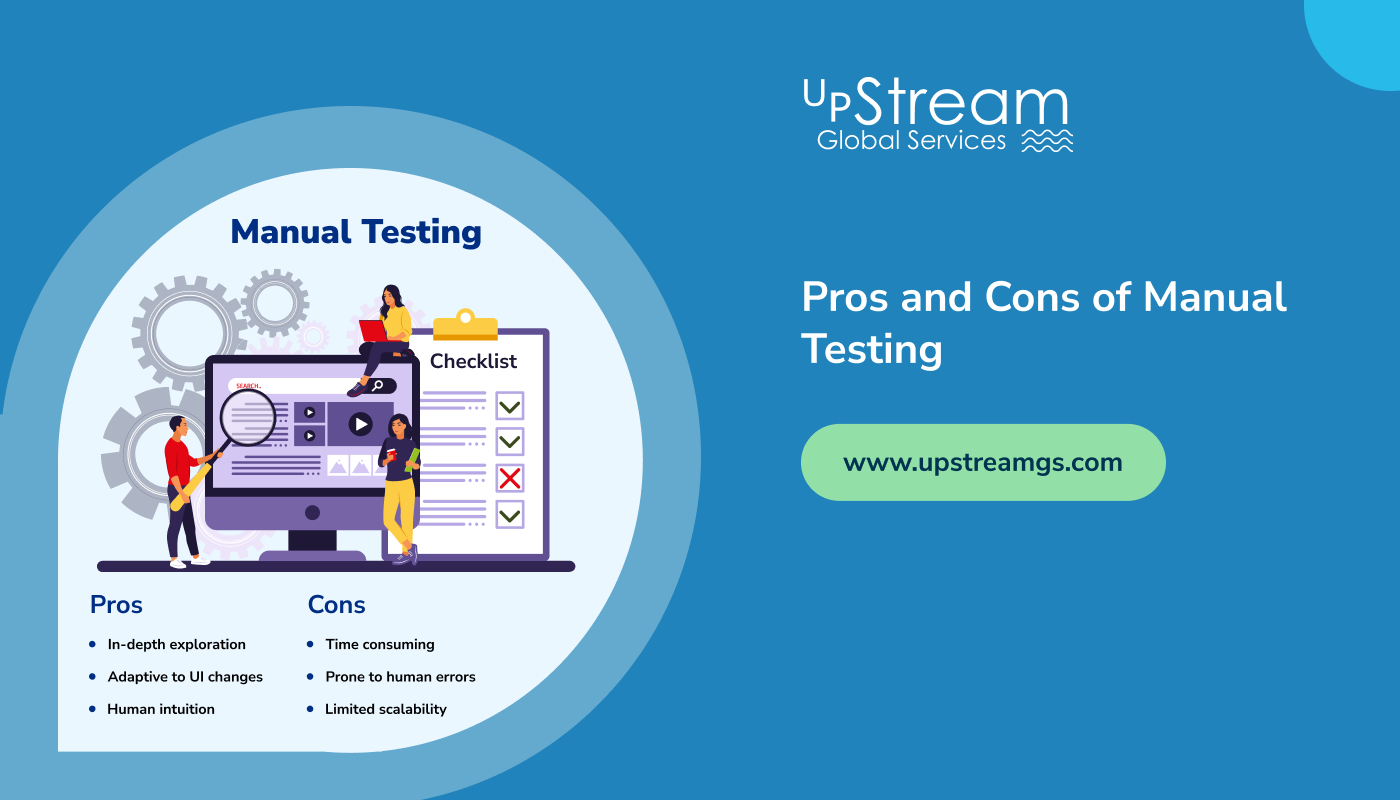
Discover the ins and outs of Manual Testing in software development. Dive into its pros including human insight and cost-effectiveness, alongside cons such as time consumption and limited test coverage.

Explore easy steps to protect your business from cyber threats. Here are the best practices for ransomware prevention, from data backup to employee education

Explore effective strategies for seamlessly integrating manual and automated testing in software development. Discover the benefits, challenges, and best practices to optimize your testing processes.”
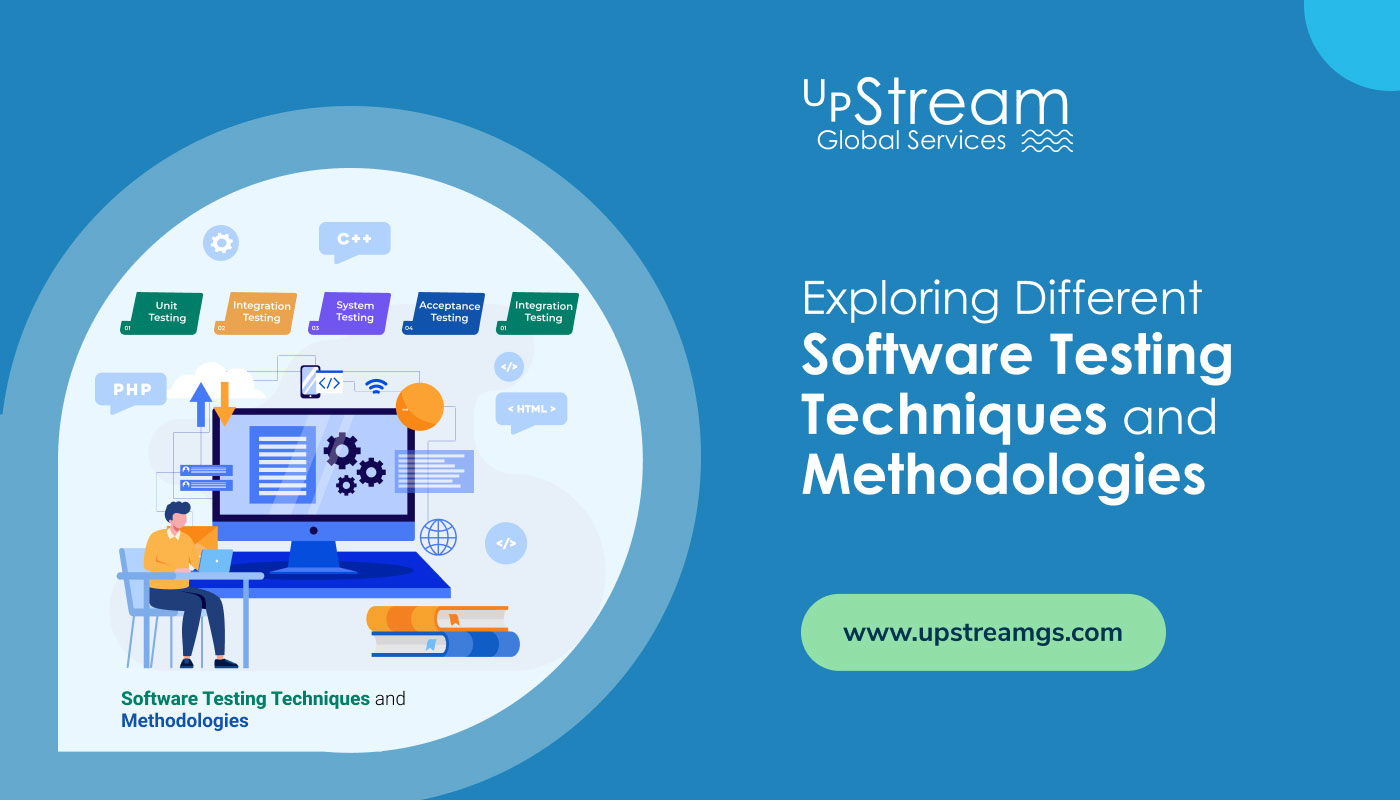
Explore various software testing techniques and methodologies, including waterfall and agile, to enhance product quality and streamline the software development process. Read the blog to find out

Table of Contents What is Functional Testing?Validating User RequirementsIdentifying Defects and BugsEnsuring User SatisfactionMethodologies of Functional TestingWhat is Non-Functional Testing?Assessing PerformanceEnsuring Reliability and AvailabilityEvaluating SecurityMethodologies of Non-Functional TestingConclusion Do you want to know the difference between functional and non-functional testing? If so, you have landed on the right page. In software development and quality assurance,… Continue reading Know the Difference: Functional Testing vs. Non-Functional Testing